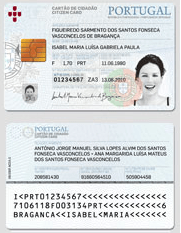
Image retrieved from http://www.cartaodecidadao.pt/
Now that you know which security mechanisms a Public Key Infrastructure can provide let’s review some cases where a PKI framework can be a security enabler. A PKI is normally deployed in a organization to fulfill a business requirement. For example the use of secure email might be one of the most popular ones. Below is a list of popular use cases that can influence the adoption and deployment of a PKI in a organization:
- 802.1x Port-Based Authentication : A client/server-based access control and authentication protocol that restricts unauthorized devices from connecting to either an 802.11 wireless network or a wired LAN. EAP-TLS is one of the 802.1x mechanisms that will support the usage of client to connect to the the network infrastructure using certificate-based authentication.
- Remote Access : Trough the usage of VPNs, remote users can connect to a private network by using a variety tunneling protocols. Certificates increase the strength of the authentication mechanisms used for either IPsec or SSL based VPNs.
- Secure Email : Majority of people will hesitate to send plans, contracts or other confidential data in unsecure envelopes trough the postal service, however they do send the same type of content tough unsecure email. Worst still is how easy is to spoof an email. By using certificates the email security will be enhanced. Using certificates its possible to verify the sender digital identity, the proof of origin and message authenticity. Plus the content can be protected trough the use of encryption.
- SET for E-Commerce Transactions : The Secure Electronic Transaction (SET) is a protocol designed for protecting credit card transactions over the Internet. It is an industry-backed standard that was formed by MasterCard and Visa (acting as the governing body) in February 1996. SET relies on cryptography and digital certificates to ensure message confidentiality and security. Note that SET failed to be adopted by the industry.
- Software protection. Digital signatures can be used to protect software. By signing the software, the integrity of the software is assured when it is distributed. The signature may be verified when the software is installed trough code signing processes to ensure that it was not modified during the distribution process and to prevent the installation of unauthorized software.
- Web Authentication and Encryption : The Secure Sockets Layer and Transport Layer Security (SSL/TLS) are cryptographic protocols for securing bidirectional communication channels. SSL/TLS are commonly used with TCP/IP. One of the most powerful advantages of these protocols is that can use certificates to do server and/or client authentication allowing mutual authentication.
- Internet Protocol security : Certificates can be used to authenticate the two endpoints participating in an Internet Protocol security (IPsec) connection. Once authenticated, IPsec can be used to encrypt and digitally sign all communications between the two endpoints. Certificates do not play a part in the actual encryption and signing of IPsec-protected data—they are used only to authenticate the two endpoints.
- Smart Card : The usage of a Smart card as a form of authentication that supports certificate-based strong authentication is ideal for critical security uses (e.g banking transactions, e-ID). Examples of such implementation is the Portuguese e-ID card which can be used to access specific applications, digital sign emails and documents with legal binding or authenticate the user. To perform these tasks, a user must possess the smart card and he needs to know its personal identification number (PIN).
- Data Encryption : Ability to encrypts data at rest by using a combination of symmetric and asymmetric encryption methods.
References:
B. Komar, Microsoft Press, Windows Server 2008 PKI and Certificate Security
B Ballad; T Ballad; E Banks , Access Control, Authentication, and Public Key Infrastructure, Jones & Bartlett Learning

